Going Beyond IT Cybersecurity Technologies to Protect the Connected Fleet
For 30 years, hackers have devised an unending stream of creative methods to gain a foothold into endpoints, servers and IT networks. Now, the connected vehicle is in the cross-hairs. Equipped with dozens electronic control units, have more than 100 million lines of code and connected to the internet, vehicles are vulnerable to cyber threats. The now-mature IT cybersecurity industry has made tremendous progress in protecting against the evolving cyber threat landscape, but how can these practices and technologies be adapted to the automotive world to protect connected cars? In this blog we will discuss the two worlds, IT and automotive, and how the advanced technologies of IT cybersecurity can be leveraged for the world of connected vehicles and fleets.
IT Cybersecurity Has Come a Long Way
Ever since the Morris worm infected the world’s unprepared cyber infrastructure in 1989, Information Technology (IT) departments have been coping with cyberattacks. Already reeling from the realization that the era of malware had begun, the rapidly growing IT cyber infrastructure was struck by a series of viruses that infected thousands of endpoints and servers worldwide. By 1990, Norton antivirus was launched and the cybersecurity industry was born.
Cyber hackers and defenders quickly became locked in a long-term duel that still shows no signs of abating. Hackers consistently demonstrate a breathtakingly brilliant level of innovation, finding every nook and cranny through which they can attack IT systems and data. Cybersecurity experts answer in kind with ingenious protection mechanisms that thwart incidents. Hardly a week goes by without news concerning the latest exploits—ransomware, theft of credit card information, malvertising and more.
Today, virtually every computer and network in the world is armored with a host of cybersecurity mechanisms like network and web-application firewalls, anti-virus programs, deep-packet inspection and sandboxes. Threat intelligence is shared across industries and countries. The IT world now spends more than $90 billion annually in information security products and services and this expenditure increases every year.
IT vs. OT Networks in the Cyber Threat Era
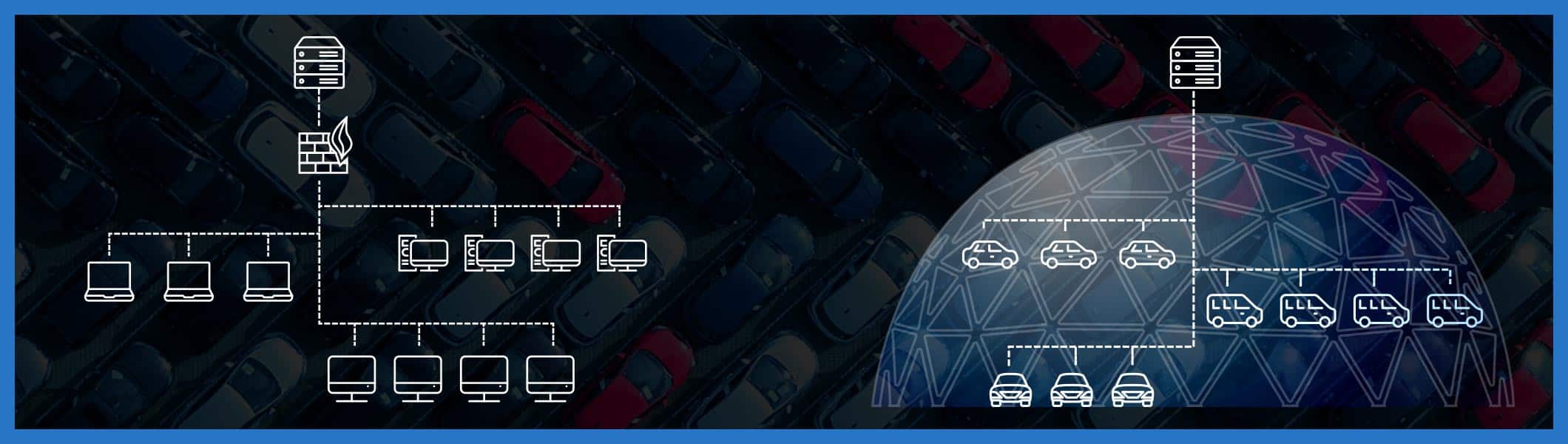
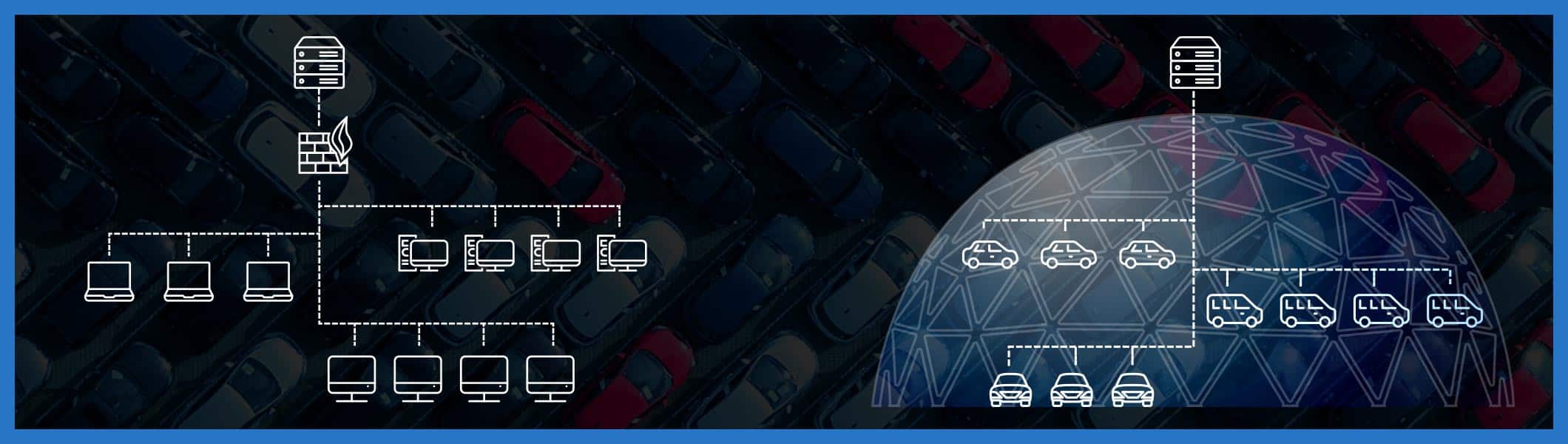
Connected fleets resemble the world of IT networks in many ways. Vehicles, with their dozens electronic control units (ECUs) and numerous other computing devices, act like endpoints that, together, process more than 100 million lines of code, generating gigabytes of data per hour, and sending and receiving volumes of data that rapidly fill server farms.
In terms of network connectivity, vehicles connect remotely to telematics backend servers, just as remote IT endpoints (e.g., employee PCs) connect remotely to enterprise servers.
In terms of cyber-breach potential, both worlds, IT and automotive, share similar vulnerabilities: a single compromised endpoint (or car) can compromise the network (or fleet), gaining a foothold to move laterally to other endpoints (cars), access servers (e.g., telematics servers) and, from there, take control of the entire network (or fleet).
Connected vehicles and telematics servers must be protected from remote hacking at least as strongly as IT endpoints and servers. Exploiting telematics servers to deliver remote commands to unlock doors, shutdown engines or disable brakes, can even cost lives. Once a hacker gets his hooks into even a single vehicle, he can go from there, via the telematics server, to shut down the fleet and demand a king’s ransom to release it.

Can Connected Fleets Adopt IT Cybersecurity Practices?
The connected-vehicle ecosystem has many lessons to learn from the mature world of IT where cyberattacks occur hundreds of thousands of times every day. Over decades, thousands of IT cybersecurity vendors have developed powerful protections against the onslaught of hackers. There isn’t an enterprise IT network without at least several of these measures in place.
The mainstays of IT security are arrays of advanced intrusion prevention, detection and response systems. Next-generation firewalls and anti-virus technologies are routinely deployed throughout the enterprise network. Since threat vectors are constantly changing and attacks are becoming more sophisticated (there are over 700 million known forms of malware in circulation and 140 million of these came to light in the past year), cybersecurity vendors have developed mechanisms to update their software products every day with the latest protection signatures derived from global threat intelligence.
There is growing awareness, however, that cybersecurity mechanisms, while necessary for the protection of individual endpoints and servers, require a more centralized and holistic approach to deal with the evolving threat landscape. Cybersecurity solution vendors like Crowdstrike and CarbonBlack have turned to a proactive approach to protect endpoints and servers, ceaselessly collecting vast quantities of data about activities, events and behaviors from all enterprise computer devices, and sending them to powerful analysis engines residing in the cloud. From there, the companies concentrate substantial computer power to plow through the big data and react with effective, holistic responses that mitigate threats across the entire IT network.
IT Cybersecurity Technologies Can’t be Implemented As-Is in Automotive Environments
Wouldn’t it be great if connected-vehicle manufacturers, Tier 1 suppliers, fleet managers and other concerned souls could simply adopt many of the technologies, along with best practices, that comprise the legion of cyber defenses that defend IT endpoints, servers, networks and information?
It’s not so simple. Although there are many similarities, there are also differences and gaps which militate against the application of these technologies to protect the connected fleet.
Vehicles pose distinct challenges when it comes to cybersecurity:
- Proprietary telematics protocols
- Addition of software and hardware to vehicles is not trivial
- Risks associated with frequent remote software updates
- Protection from fraud and fleet business-policy violations
Proprietary Telematics Protocols
The telematics industry is exploding. Mind-boggling market predictions are encouraging numerous players from many industries to enter the field with their version of how telematics units should behave. Every automotive OEM carries one or more telematics system, each with its own proprietary telematics protocol. A single fleet may comprise vehicles with telematics units from several vendors with the need to support numerous proprietary protocols. Securing the telematics communication channels requires specialists who undertake to learn the broad, untamed market of today’s and tomorrow’s telematics solutions. Today’s IT cybersecurity solution do not deal with these capabilities.
Addition of Software and Hardware to Vehicles is Not Trivial
Unlike installing anti-malware software on PCs, a trivial and common practice, implementing new security software or hardware into vehicles requires close collaboration with OEMs throughout the entire design and production cycles. Because these cycles take years to complete, they do not address the vulnerabilities of the millions of cars and fleets already in production or on the road.
Risks Associated with Frequent Remote Software Updates
Unlike PCs, where security updates occur on a daily basis, applying remote OTA updates to vehicles at such a frequency can suffer bugs or other issues with the implementation. Vehicles on the road cannot afford a bad or missed OTA that could open a cybersecurity hole or shut down the vehicle, costing money and time, or worse, endangering lives.
Protection from Fraud and Fleet Business-Policy Violations
In addition to protecting against cyber-attacks, IT cybersecurity solutions, such as network firewalls, offer manual security-policy configuration to enforce what is and is not allowed in the network. How can such policies be applied to the automotive environment where one must not only understand proprietary application-level telematics server commands and vehicle messages, but also the complex context of the vehicle (i.e., is it driving? parking? etc.)? IT cybersecurity solutions are simply not designed to do that.

A New Approach: Centralized Automotive Cybersecurity
Just as the centralized, cloud-based approach mentioned above is gaining traction in IT cybersecurity, it has a vital place in fleet security as well, but with adaptations to meet automotive-specific requirements. The centralized security approach would be to collect the telematics, vehicle performance and other data sent from vehicles or other sources, such as mobile apps (just as car manufacturers and connected fleets are doing today anyway) and employ a cloud-based, centralized, powerful system to correlate and analyze the data using the most advanced AI and machine learning technologies.
The pure ‘horsepower’ and other capabilities of such cloud-based technologies can inexpensively keep abreast of the latest technologies. They are always able to cope with the vehicle cybersecurity challenges of the day. Furthermore, this approach eliminates the need to apply security updates to the fleet vehicles. Concentrating many aspects of cybersecurity in the cloud is a far more efficient strategy than attempting to keep thousands or millions of cars up to date using frequent OTA updates. It also eliminates the need to deploy complicated in-vehicle solutions, so that vehicles already on the road can benefit from the latest protections.
Another major benefit is the visibility and protection across the entire fleet, not having to protect vehicles one by one. By collecting data from all fleet vehicles in a central database, cyber-attacks can be stopped in their tracks before they can spread across the fleet. In addition, by examining fleet-wide data, anomalies in fleet behaviors (not just individual vehicles) can be detected. For example, if an “unlock door” command is sent to 100 vehicles simultaneously at 2 AM within a 10KM radius, this could indicate that a hacker has gained control over the telematics server and is conducting a remote, fleet-wide attack.
Still another level of protection that is unobtainable using IT cybersecurity methods is the ability to track vehicle behaviors, enabling detection of fraud and violations of fleet policies (or business rules). Consider a situation where a certain driver is employing a rental car to provide a taxi service—a violation of the rental agreement. How would the rental company find out before it’s too late? By conveying the vehicle’s telematics data to the cloud, analysis engines can automatically track the use of the car to spot behaviors, such as how often a vehicle starts and stops, driving patterns and more, to flag a violation.
Upstream Delivers Cloud-Based Cybersecurity for Connected Vehicles and Fleets
Upstream’s approach involves a non-intrusive, cloud-based security offering that stays current with advancements of cybersecurity technologies without having to penetrate the vehicles themselves. It ‘understands’ and inspects the application layer of propriety telematics protocols and examines the transmissions between vehicles and backend servers and other sources. It provides alerts for undesired or suspicious communications. Upstream protections and policies are always and automatically kept up to date utilizing Upstream’s unique automotive cybersecurity threat intelligence technology, eliminating the need to update vehicles remotely. In addition, Upstream leverages its analytic capabilities to detect fraud and violation of fleet policies in vehicles offered by rental, leasing, commercial fleets and ride-sharing services.
To learn more, visit upstream.auto