[By Yoav Levy, Co-Founder and CEO]
Between SpaceX, Tesla, the Boring Company and many other initiatives, Elon Musk is, to say the least, busy. Despite working up to 100 hours a week, he still has time to worry about a fleet-wide hack on Tesla. And rightly so.
All large vehicle manufacturers and many Tier 1 suppliers are making big investments in connected and autonomous vehicle technology and, like Musk, they understand the need to build-out new security infrastructures for their fleets to ensure they are safe from cyber-attacks.
Protect the fleet and not just the car
KPMG recently released their report, ‘Protecting the fleet – and the car business’. It highlights the need for car manufacturers (OEMs) and businesses which manage vehicle fleets to adopt a completely fresh security framework.
Today, the average car contains more than 150 million lines of code written by dozens of different vendors, multiple computers and vast quantities of wireless connections to internal and external communication channels. This, together with the data-hungry nature of cars and their users (according to the report during 2017, North American users consumed an average of 6.9 gigabytes each month) and the impending 5G roll out, is expected to create an explosion of in-car technology innovation and confirms we are firmly in the age of ‘the Internet of Cars’ (IoC).
Although this technology revolution has extraordinary benefits for car users and indeed businesses with fleets of cars, there is also a major sticking point – the issue of electric vehicle cyber security. The report notes that ‘many manufacturers have made huge strides in addressing cyber security issues within their vehicles, taking various approaches to the challenge even as the threat landscape continues to evolve, and solutions continue to emerge and mature’.
The next disruptive threat: fleet-wide cyber-attacks
Crucially, these developments do not address the far more frightening possibility of a fleet-wide cyberattack or hack, and that has Elon Musk worried. This, according to KPMG, represents the next disruptive threat to the automotive industry. The threat comes in many shapes and sizes, including vehicle consumer data breaches, DoS attacks, malicious exploit attempts, intellectual property theft and the safety of drivers and passengers. A fleet wide cyber-attack has the potential to cause cataclysmic damage.
Today, a car can be forced to swerve across lanes and travel over 120 miles per hour while the driver is totally powerless to stop it from happening. That’s a frightening image on its own, let alone the scenario where a fleet of hundreds of vehicles in different locations can be simultaneously controlled. We’ve seen the use of vehicles in terrorist attacks rise significantly in recent years, but we are yet to witness a remotely controlled vehicle army. To prevent this from becoming a reality, it is essential that fleet-wide security is taken seriously, and automotive network protection is prioritized.
According to KMPG (and I agree), ‘cyber security can no longer be seen as a corporate challenge. It is a much broader and more complex engineering, production and operational task – and it requires a new approach’. With 65 million connected cars on the road today without security, multidimensional systems that cover the individual vehicle, the connected fleet, the automotive business and the supply chain will be essential – particularly as this figure is expected to rise to 250 million by 2020.
“Analyzing the entire fleet-level data offers full visibility into the fleet’s security posture. By understanding the complete picture, normal car and driver behavior can be monitored effectively and attacks can be prevented before they reach the network and cause harm.”
Yoav Levy, Co founder and CEO, Upstream
Monitor, analyze and protect: from within the data center
So, what can you do to protect your fleet? That’s where we come in. Our centralized cloud platform sits in the data center and permits the entire fleet to be monitored and protected with a combination of big data analytics and advanced cyber and fraud security technology.
Upstream’s Fleet Cybersecurity Platform enables access to automatic protection through the use of health dashboards (offering alerts on cyber threats, policy violations and additional infrastructure indicators) for the fleet. Additionally, analytics captured from all levels of the fleet architecture – car, driver, mobile app and server – help fleet operators investigate an incident and determine the cause so that similar situations can be prevented in the future. This centralized, automated and insightful approach is the key to securing fleets of connected cars in the future.
Analyzing the entire fleet-level data offers full visibility into the fleet’s security posture. By understanding the complete picture, normal car and driver behavior can be monitored effectively and attacks can be prevented before they reach the network and cause harm.
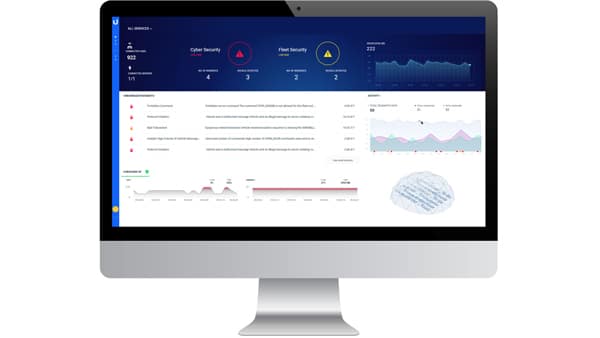
UPSTREAM’S DASHBOARD – AUTOMOTIVE FLEET SECURITY HEALTH AT A GLANCE
And by making use of a secure boundary in the demarcation point between the operational network and the IT network, users can ensure protection of the communication data between the vehicles and command and control servers. Upstream leverages deep protocol understanding of the communications between data centers and fleets to detect, interpret and alert in real-time of any threats to the fleet.
As the world we live in rapidly changes, it’s clear that automotive cybersecurity must keep up with the pace of technology, sociological and environmental development. The risk of a fleet cyber security attack is grossly underestimated and there are very few solutions that sit above proprietary protocol. Businesses must start to take this risk seriously and protect their fleet efficiently so that they can be prepared for the next generation of automotive security breaches – which are just around the corner.