Ready to Keep Up with Smart Mobility? The Effects of Connectivity on the MaaS Ecosystem
When you’re in the eye of the storm, most chances are you’re not going to be able to see the outcome of that storm. And being in the automotive industry today is exactly what that’s like; the industry is undergoing rapid transformation and becoming a smart mobility ecosystem. Connectivity is at the foundation of this ecosystem, basically enabling any type of value-added services that can be built on top of connected cars. With nearly daily mobility technology announcements, and both regulators as well as investors looking to predict the consequences – a massive change is surely upon us.
The automotive industry, as part of the overall transportation industry, is undergoing a drastic transformation, probably different than anything we’ve ever experienced in this sector. Growing technological trends, namely digitalization, IoT, urbanization, Autonomous tech, and shared economy, are all completely disruptive business models reshaping this industry. Without going into the endless debate over what came first; the innovative technologies or the new generation of users expecting new types of services – it’s clear that three interconnected processes are now happening:
- Advanced technologies are introducing new servicing options, gradually turning products into services
- Drivers are turning into users even in traditionally hardware-oriented sectors such as the automotive industry
- Connectivity is growing, and with it, the cyber-attacks surface is expanding, demanding new security standards in these uncharted territories

The Rise and Effects of MaaS – Mobility as a Service
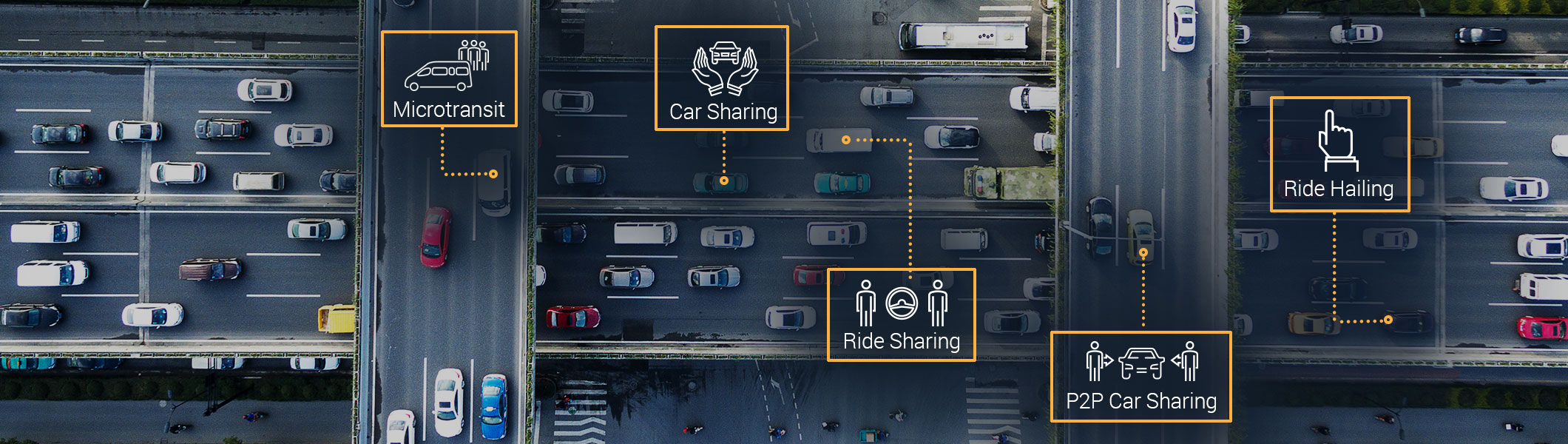
These trends, along with others, have all led to the emergence of what we call today Mobility-as-a-Service (MaaS). MaaS essentially provides the flexibility required in today’s on-demand environment. The automotive industry is rapidly adjusting to people who value experience over possessions, and thus shifting its focus from a car-centric approach to a user-centric one, offering a new generation of digital and connectivity services. However, this shift isn’t easy for all stakeholders in the industry –
Seeking New Competitive Advantages in the MaaS Landscape
As soon as shared and smart mobility services have entered the market, car makers have immediately started to experience a ‘big bang’ moment. With every shared car getting 10 vehicles off the road, and over 20 million vehicles estimated to be removed annually by 2025, OEMs had a lot to worry about. In this new landscape of innovative mobility services, OEMs had to find ways to stay competitive. And so they started manufacturing connected cars with digital and remote connectivity services (such as the Audi Q5 or the Tesla Model S), as well as partnering more closely with TSPs in order to provide new digital services (just like Chevrolet Cruze and GMC Terrain with their OnStar connectivity system, or VOLVO and SUBARU with their WirelessCar connectivity services).
In this race towards advanced mobility services, the connected car service instantaneously became vulnerable to increasingly sophisticated cyber-attacks – targeting connected vehicles, their backend servers, and any app connecting the two. In other words, the attack surface has massively expanded, and dangerous security breaches aim to tumble this whole house of cards with safety, personal data, and sensitive corporate data – all on the line.
Smart Mobility Cannot Succeed Without Security
What makes cybersecurity a top concern in the connected car ecosystem today is perhaps its immediate association with safety. This time we’re not “just” talking about data privacy and corporate IP as a target, but first and foremost about people’s safety – both drivers and their passengers. In this industry, securing the connected car is what keeps these human lives safe, which is why every vulnerability found in a mobile app, a backend telematics server or a car’s in-vehicle computers could have disastrous implications.

That’s exactly why TSPs, OEMs, and regulators are all joining hands, not just in increasing revenues and providing new services, but also in protecting the connected car. However, because of the complexity of multiple stakeholders providing services for the same connected car (for example, an OEM hiring a TSP to provide connectivity services for the connected car), securing only the vehicle or the backend server alone is not enough; the entire value chain in the smart mobility services has to be secured. The data fed by the connected vehicle to the backend servers, and then all the way back to the vehicle via any intermediate third-party app (such as DriveSync or Ignite) – this entire data flow needs to be meticulously monitored and analyzed by the most advanced AI technologies, in real-time, to report on any suspicious activity while it is happening.
Comprehensive Security Approach to Protect the Entire Connected Car Ecosystem
Changing technological landscape has given rise to innovative connected car platforms and new services that allow users of the connected cars (whether corporate or private) to experience the latest in smart mobility features. But none of these technologies can be properly used without a comprehensive security solution, providing visibility into all possible entry points across the communication flow, allowing proactive measures in real-time, and ultimately helping OEMs, TSPs and commercial car-fleets to keep their drivers and family members safe.